Products
Solutions
Resources

Today, the sheer volume of cybersecurity vulnerabilities exceeds what manual processes can handle. Vulnerability exploitation surged by 180% year-over-year, now accounting for 14% of all breaches according to Verizon's 2024 Data Breach Investigations Report. Yet, organizations still take an average of 55 days to patch just half of their critical vulnerabilities, leaving a dangerous window for attackers. Traditional approaches can't keep pace, but AI vulnerability management offers a path forward.
Rather than leaving security leaders overwhelmed by data, AI vulnerability management transforms raw scanner data into prioritized insights that align technical risks with business impact.
This in-depth guide explains how AI-driven vulnerability management helps security teams move from reactive patching to proactive risk prevention:

AI vulnerability management is an automated approach to identifying, assessing and fixing security weaknesses across an organization's IT infrastructure. The technology uses machine learning, natural language processing and predictive analytics to automate the identification, prioritization and remediation of security vulnerabilities.
Unlike traditional vulnerability scanners that flag potential issues, AI-powered systems analyze vulnerabilities within a business context, assess real-world exploitability and recommend prioritized remediation actions based on actual risk to critical assets.
Security teams using conventional vulnerability management face several obstacles that slow response times and create blind spots in their defense posture.
Organizations manage millions of vulnerabilities across cloud, on-premise and endpoint environments. Security teams receive thousands of new common vulnerabilities and exposures (CVEs) annually, most of which lack the context needed to determine which ones pose real risk to their environment. Without AI-powered correlation, analysts waste hours investigating alerts that don't apply to their infrastructure or represent minimal actual risk.
Chief information security officers (CISOs), vulnerability management analysts and chief information officers (CIOs) feel this pain most acutely. The sheer volume creates decision paralysis, where teams either attempt to patch everything or rely on incomplete risk assessments that miss critical exposures.
Human analysts manually reviewing vulnerability reports introduce a lag between detection and remediation. Vulnerability management analysts and compliance teams spend days:
This manual triage process extends mean time to remediation (MTTR) from hours to weeks, giving attackers ample opportunity to exploit known weaknesses.
Traditional scanners report vulnerabilities without understanding the business context. A critical vulnerability in a development server receives the same urgent flag as an identical issue in a customer-facing payment system, despite a different business impact.
CISOs struggle to communicate actual risk to boards when technical severity scores don't align with operational reality. Vulnerabilities remain untied to asset value, data sensitivity or operational criticality, making prioritization largely guesswork.
Conventional tools flag issues only after they're discovered and published, leaving organizations perpetually behind the threat curve. By the time a CVE appears in scanner results, attackers may have already weaponized the exploit.
Security teams operate in constant catch-up mode, patching yesterday's vulnerabilities while tomorrow's attacks bypass their defenses. This reactive posture is felt across all security personas, from security operations center (SOC) managers to board members demanding better risk prevention.
Security findings don't translate into business language that executives understand. CISOs and chief revenue officers (CROs) face boards asking, "What does this mean for our operations?" without clear answers.
Technical reports filled with CVE numbers and common vulnerability scoring system (CVSS) scores fail to convey financial impact, operational disruption or competitive risk. This translation gap undermines security program investment and slows decision-making when quick action matters most.
Traditional approaches lack standardized, auditable metrics to measure security program effectiveness. As a result, CISOs, CFOs and CROs struggle to justify vulnerability management investments without clear evidence of risk reduction. Without clear performance indicators, security remains a cost center rather than a value driver.
Vulnerability scanners, patch management systems and IT service management (ITSM) platforms operate in isolation without sharing data or coordinating remediation workflows.
SOC managers and risk management teams juggle disconnected tools where scanner findings don't automatically generate ITSM tickets, and patch systems can't prioritize based on those results.
AI transforms vulnerability management from a data collection problem into an intelligent risk-reduction engine. Machine learning and automation address each traditional challenge with capabilities that scale beyond human analysis capacity.
AI systems process massive vulnerability datasets that would overwhelm human analysts. Machine learning algorithms ingest data from multiple sources, including:
These systems correlate findings, eliminate duplicates and filter out vulnerabilities that don't apply to your specific environment.
The results? Security leaders see a clear vulnerability landscape. AI reduces alert fatigue by surfacing only exploitable, business-critical issues that demand immediate attention.
Machine learning models analyze historical exploit data, patch success rates and asset criticality to generate dynamic risk scores that reflect actual threat potential. These models consider multiple factors that traditional CVSS scores ignore:
Automated validation reduces false positives that consume analyst time. AI engines verify vulnerabilities through multiple data points before escalating alerts, eliminating the hours teams spend confirming whether a flagged issue represents genuine risk.
AI introduces the business context that traditional scanners lack. Contextual scoring models integrate technical vulnerability data with asset inventory, business service mapping and data classification. The system understands that a critical vulnerability in your customer database represents a higher risk than the same issue in an isolated test environment.
Machine learning links vulnerabilities to specific business services and operational impact. When a vulnerability appears in the web server supporting your e-commerce platform, AI can correlate it with revenue data, customer traffic patterns and regulatory compliance requirements.
This business alignment helps CISOs explain risk in terms executives understand: potential revenue loss, compliance penalties or operational downtime.
AI enables predictive security operations through threat intelligence integration and behavioral analysis. Machine learning models study exploit patterns, attacker tactics and emerging threat campaigns to anticipate which vulnerabilities will become targets before public disclosure.
Anomaly detection identifies unusual system configurations or network behaviors that indicate latent vulnerabilities that conventional scanners miss. AI spots deviations from baseline that suggest security weaknesses, even when no published CVE exists yet.
Additionally, continuous monitoring ensures new vulnerabilities are identified immediately. This allows organizations to shift from periodic snapshots to real-time visibility, patching vulnerabilities during the critical window before attackers develop reliable exploits.
AI platforms generate business-aligned visualizations and executive summaries from complex technical data. Natural language generation creates board-ready reports that explain vulnerability risk in operational and financial terms. Instead of presenting CVE lists, AI produces narratives describing how vulnerabilities threaten specific business objectives, compliance requirements or customer commitments.
Automated dashboards translate technical metrics into business performance indicators. Boards see meaningful data like "percentage of high-risk vulnerabilities mitigated within 48 hours" or "reduction in exposure to actively exploited vulnerabilities."
AI analytics transform security outcomes into quantifiable business metrics. Trend analysis shows a reduction in risk exposure over time, proving the security program's effectiveness.
Machine learning quantifies how vulnerability mitigation affects operations and financial risk. AI models calculate potential cost avoidance by showing which prevented exploits would have caused data breaches, system downtime or regulatory penalties. These calculations give security leaders concrete ROI data.
AI serves as an integration layer connecting vulnerability scanners, IT service management platforms, patch management systems and configuration management databases. Data flows automatically between systems, eliminating manual transfer and errors while correlating vulnerability data across cloud, on-premise and hybrid environments for complete infrastructure visibility.
Automated workflows orchestrate remediation from detection through resolution. When AI identifies a critical vulnerability, it automatically creates tickets, assigns them to appropriate teams and tracks progress through completion with full audit trails for compliance.
AI enhances each phase of the vulnerability management lifecycle, transforming manual, error-prone processes into automated, intelligent operations. Understanding how AI improves each stage helps organizations implement solutions that deliver measurable results.
Traditional discovery relies on periodic scans that produce incomplete asset inventories and miss newly deployed systems. Shadow IT, unauthorized devices and ephemeral cloud resources often escape detection. Analysts spend time reconciling conflicting asset data from multiple tools and verifying whether flagged systems still exist.
AI-driven discovery continuously maps assets using machine learning that recognizes patterns and relationships between systems, configurations and network behaviors. The technology:
This creates a complete asset inventory with real-time vulnerability detection.
Older vulnerability management approaches produce CVSS scores based purely on technical severity, regardless of whether exploit code exists, whether the affected system is exposed to the internet or whether it contains sensitive data. Security teams manually research each finding to determine actual risk, a process that takes hours per vulnerability.
AI risk scoring considers multiple contextual factors: whether working exploit code exists in the wild, what data the system contains, which business services depend on it, whether the vulnerability is actually exploitable in your specific configuration and whether attackers are actively using it in current campaigns.
Many remediation approaches rely on manual ticket creation, lengthy review cycles and coordination between security and IT operations teams. Vulnerabilities sit in queues awaiting triage, assignment and scheduling, while patches get tested in isolation without understanding dependencies or potential conflicts.
AI-powered automation ranks remediation tasks based on risk analysis, suggests optimal patching sequences that minimize operational disruption, automatically creates and routes tickets to the appropriate teams, and monitors systems post-patching to confirm that vulnerabilities are resolved without causing new issues.
Traditional monitoring occurs through periodic scans that provide snapshot views of security posture. Vulnerabilities discovered between scan cycles go undetected for weeks or months, while verification relies on manual checks that confirm patches deployed successfully.
AI agents constantly scan for emerging cyber threats, configuration changes that introduce vulnerabilities and new assets requiring security assessment. The technology:
This provides visibility with automated validation that vulnerabilities remain fixed and no new gaps emerge between remediation cycles.
Traditional reporting requires manual data compilation, spreadsheet manipulation and custom presentation creation. Security analysts spend hours or days preparing board reports, compliance documentation and management dashboards that quickly become outdated as new vulnerabilities emerge.
AI generates board-ready summaries from technical vulnerability data using natural language generation, explaining security posture in business terms. Real-time dashboards provide instant visibility into current remediation status, trending risk exposure, and team performance, while automatically generating required reports for frameworks such as PCI DSS, HIPAA, SOC 2, and GDPR.
Each stakeholder receives information appropriate to their role, freeing security teams to focus on risk reduction rather than report generation.
While AI transforms vulnerability management capabilities, it also introduces new risks, dependencies and ethical dilemmas that security leaders must navigate. Organizations deploying AI-powered vulnerability management need strategies to address these concerns.
AI's accuracy depends on the quality and diversity of its training data. When training data underrepresents certain asset types, industries or operating environments, AI may misjudge exploit likelihood or overlook critical vulnerabilities.
Models trained primarily on historical data may reinforce legacy risk patterns while failing to account for emerging technologies like containers, serverless functions or operational technology environments.
Businesses must audit data pipelines feeding AI systems, retrain models on diverse data sources representing their complete infrastructure and maintain human oversight for high-stakes decisions. Regular validation against known vulnerabilities ensures AI recommendations align with security expert judgment.
Many AI vulnerability management systems operate as "black boxes" where security teams can't understand why the model assigned specific risk scores or prioritized particular vulnerabilities.
This opacity creates trust issues when analysts must defend prioritization decisions to stakeholders or explain why certain vulnerabilities received lower priority despite high CVSS scores.
To prevent this, CISOs should select AI platforms offering explainable AI capabilities that document reasoning behind risk scores and prioritization decisions. Systems should show which factors influenced each assessment, allowing analysts to verify logic and explain decisions to stakeholders while preserving human oversight for critical decisions.
AI vulnerability management platforms must integrate with existing security tools, IT service management systems and configuration management databases. Poor integration creates new silos rather than breaking down existing ones, while integration projects often require significant customization that extends implementation timelines and increases costs.
That’s why organizations should evaluate AI platforms' native integrations with their existing tools before selection, prioritize vendors offering pre-built connectors for common systems and establish clear integration requirements during vendor evaluation to avoid operational disruption and excessive total cost of ownership.
Organizations may develop over-dependence on AI systems, diminishing human expertise in vulnerability assessment and risk analysis. As AI handles routine prioritization, security analysts may lose the skills needed to evaluate vulnerabilities manually when AI systems fail or produce questionable results, creating single points of failure.
Organizations should view AI as an augmentation rather than a replacement for human expertise. Training programs should maintain analyst skills in manual vulnerability assessment and risk analysis, while regular exercises validate AI recommendations against manual analysis to preserve critical thinking.
AI vulnerability management systems process sensitive information about organizational infrastructure, security weaknesses and business operations. Cloud-based AI platforms transmit vulnerability data to external systems, creating exposure risk, while data protection regulations may restrict the sharing of certain vulnerability information with third-party AI services.
Considering the above, you should evaluate AI platform security and data protection practices before adoption, understand where data is processed and stored, and implement appropriate data classification and access controls. You should also consider on-premises or private-cloud AI deployments for sensitive environments, and ensure AI platform compliance with relevant data protection regulations.
While AI vulnerability management benefits organizations of all sizes, enterprise and SMB companies approach adoption differently based on distinct operational realities, resource constraints and security maturity levels.
Organizations of all sizes share core benefits from AI-driven vulnerability management:
Enterprise organizations operate at a scale where AI becomes essential rather than optional. A single enterprise might track 50,000+ assets spanning on-premise data centers, multiple cloud platforms, regional offices and remote endpoints.
The complexity of global infrastructure, distributed teams and sophisticated threat landscape makes manual vulnerability management mathematically impossible.
AI addresses several critical enterprise challenges:
Small and mid-size businesses face distinct vulnerability management challenges requiring different AI capabilities than those enterprises deploy. Most SMBs operate with one or two security professionals juggling vulnerability management alongside day-to-day IT support, network administration and application deployment.
AI helps SMBs overcome key constraints:
Selecting the right AI vulnerability management platform requires evaluating capabilities against your organization's specific needs, existing infrastructure and security maturity. These considerations help organizations identify solutions that deliver value.
The AI platform must connect with your current vulnerability scanners, ITSM tools, configuration management databases and security orchestration systems. Evaluate native integrations with tools you already use. Poor integration creates another data silo rather than breaking down existing ones.
The platform should explain how it generates risk scores and makes prioritization decisions. AI that provides recommendations without reasoning undermines analyst trust and makes it impossible to defend decisions to stakeholders or auditors. Look for systems offering decision trees, factor weighting and confidence scoring that document assessment logic.
AI vulnerability management requires business context, not just technical severity. The platform should incorporate asset criticality, data sensitivity, business service dependencies and regulatory requirements into risk calculations. Generic CVSS scoring without environmental context produces alert fatigue.
AI should automate repetitive tasks while preserving human oversight for critical decisions. Look for platforms that create and route remediation tickets, suggest remediation actions based on successful past resolutions, verify patch deployment and vulnerability closure and generate compliance reports without manual data compilation.
The platform must handle your current environment volume while scaling to accommodate growth. Evaluate whether the system can process your asset count and vulnerability volume without performance degradation, and understand how the platform scales as you add cloud environments or acquire companies. Additionally, verify whether pricing models make scaling economically feasible.
AI vulnerability management requires ongoing optimization to maintain effectiveness. Evaluate the vendor's security expertise and understanding of:
Additionally, assess the responsiveness of technical support and the availability of professional services for implementation and optimization.
The platform should support compliance frameworks relevant to your industry. Verify that the system generates evidence and reports for regulations you must meet, understand whether the platform itself has relevant certifications (SOC 2, ISO 27001, FedRAMP) and evaluate data residency and protection capabilities for regulated industries.
Understand the total cost of ownership beyond initial licensing fees. Consider implementation costs, integration customization, ongoing maintenance and support, training requirements for staff and costs to scale as your environment grows.
Vendors should demonstrate clear ROI through metrics such as reduced MTTR, fewer analyst hours spent on manual triage, and fewer security incidents from faster patching.
Technologies and evolving threat landscapes reshape how organizations approach vulnerability management. Understanding these trends helps security leaders prepare for the next generation of AI-powered defensive capabilities.
The next evolution in AI vulnerability management is likely to involve agentic systems that operate with increasing autonomy while maintaining appropriate human oversight.
Agentic AI vulnerability management uses autonomous agents that can research vulnerabilities, correlate threat intelligence, prioritize risks and initiate remediation workflows without continuous human direction.
Unlike current AI systems requiring humans to review and approve each step, agentic AI could make routine decisions automatically while escalating novel or high-risk scenarios to human experts.
Modern AI systems will better anticipate which vulnerabilities attackers will weaponize before exploitation occurs at scale. Advanced machine learning models could analyze attacker behavior patterns, dark web discussions and proof-of-concept code publication to forecast emerging threats with increasing accuracy.
This enables organizations to patch vulnerabilities during the critical window between discovery and widespread exploitation.
AI-driven remediation may evolve beyond prioritization toward systems that automatically deploy patches and apply fixes without human intervention for low-risk scenarios. Self-healing infrastructure could detect vulnerabilities, validate patches and deploy fixes during maintenance windows autonomously.
Organizations will likely adopt automated remediation gradually, starting with non-critical systems and expanding to more sensitive infrastructure as confidence grows.
The emergence of quantum computing will likely introduce new vulnerability classes as quantum computers potentially break current encryption standards. AI vulnerability management systems may need to identify quantum-vulnerable cryptography across organizational infrastructure and coordinate migration to quantum-resistant alternatives at unprecedented scale.
Organizations managing cyber risk across fragmented tools and disconnected data sources struggle to maintain comprehensive visibility. Diligent's IT Risk Management (ITRM) platform solves this challenge by creating a cyber risk hub that unifies vulnerability data, threat intelligence and risk assessment into a single source of truth.
The platform's AI-powered integration layer breaks down silos by pulling data from any cybersecurity tool or source into one centralized hub. Organizations using vulnerability scanners can aggregate findings alongside threat intelligence, security scorecard data and configuration management information. This approach eliminates manual data consolidation, which consumes security team time and introduces errors.
Real-time vulnerability monitoring enables organizations to identify emerging trends and threats as they develop rather than during periodic scan cycles. The generic integration layer connects with third-party vulnerability tools to provide complete visibility across cloud, on-premise and hybrid environments. Security teams gain a comprehensive view of their attack surface without managing multiple disconnected consoles.
The Diligent One Platform centralizes IT risk and compliance efforts with real-time insights and automated workflows. Organizations automate control testing, unify asset and vulnerability data and meet regulatory demands ranging from FedRAMP to NIS2 without manual evidence collection. The platform helps security teams guard against cyber threats using integrations and APIs with third-party security tools.
Asset database and vulnerability aggregation provide a consolidated inventory of IT assets with real-time vulnerability insights. Security teams finally answer the fundamental question: What are we exposed to right now?
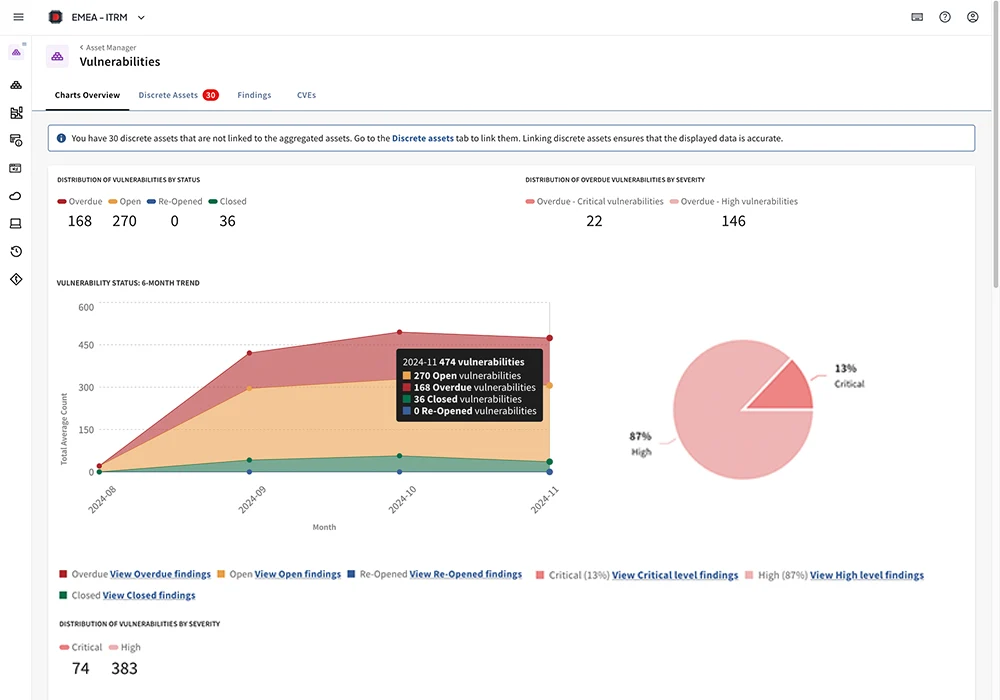
Vulnerability import from any scanner centralizes and normalizes vulnerability data directly on the platform. Through intuitive dashboards, IT teams gain access to predictive, preventive, and responsive analytics, empowering both daily operations and strategic planning.
Organizations benefit from instant visibility into their cyber threat landscape. This enables proactive prevention, swift identification, and effective remediation of risk across all IT and information assets.
Diligent’s business-aligned reporting capabilities transform technical vulnerability data into board-ready insights. Executives receive clear, actionable intelligence about cyber risk without wading through technical CVE details. This capability helps CISOs communicate security posture improvements and justify investment using metrics stakeholders actually understand.

This focus on board-level cyber risk governance recently earned Diligent recognition from Datos Insights with the 2025 Cyber Impact Award for Best AI-enabled Capability for Board-level Cyber GRC Solution. The award specifically recognizes excellence in leveraging artificial intelligence to enhance cyber risk governance, reporting and oversight at the board level within financial services organizations.
By unifying vulnerability data, automating compliance validation and translating technical risks into business language, Diligent ITRM creates the centralized intelligence layer that security leaders need to move from reactive vulnerability management to proactive cyber risk strategy.
Traditional vulnerability management drowns security teams in alerts while leaving critical risks unaddressed. Diligent's AI-powered ITRM platform cuts through the noise, delivering the focused intelligence you need to protect what matters most.
Discover how Diligent creates a unified cyber risk hub that transforms fragmented vulnerability data into actionable insights. See the platform in action.
Vulnerability management is critical because unpatched vulnerabilities represent the primary entry point for cyberattacks. Organizations face tens of thousands of new vulnerabilities annually, and attackers automate exploitation of known weaknesses within hours of public disclosure.
Without systematic vulnerability identification, prioritization and remediation, organizations leave doors open for data breaches, ransomware, system compromises and regulatory violations.
Agentic AI vulnerability management uses autonomous intelligent agents that independently research vulnerabilities, correlate threat intelligence, prioritize risks and initiate remediation workflows with minimal human intervention. Unlike traditional AI systems requiring human approval for each action, agentic systems make routine decisions autonomously while escalating novel or high-risk scenarios to human experts.
AI transforms risk-based vulnerability management by incorporating business context that traditional approaches ignore. Machine learning models analyze multiple risk factors simultaneously: technical severity, exploit availability, asset criticality, data sensitivity, compensating controls, threat intelligence and business impact.
This contextual analysis produces dynamic risk scores that reflect the actual threat to organizational operations rather than generic CVSS ratings. The result is prioritized remediation plans focused on vulnerabilities combining high technical severity, active exploitation and significant business consequences aligned with business priorities.
Effective ROI metrics for AI vulnerability management include:
Additional valuable metrics include analyst time savings from automated triage and prioritization, reduction in false positives requiring investigation, cost avoidance from prevented security incidents and compliance audit findings showing improved security posture.
AI vulnerability management platforms increasingly offer built-in mapping to established risk frameworks. Systems can automatically tag vulnerability management activities to specific NIST Cybersecurity Framework controls, ISO 27001 requirements or FAIR risk factor analysis components.
This automated mapping ensures that vulnerability identification, assessment, and remediation activities produce the evidence required for framework compliance.
AI isn’t going to replace human security analysts. AI augments rather than replaces human security analysts in vulnerability management. Machine learning excels at processing vast data volumes, identifying patterns and automating repetitive tasks that consume analyst time.
This allows security professionals to focus their expertise on strategic risk decisions, novel threat analysis and security program development. They retain responsibility for validating AI recommendations, handling edge cases outside model training data, communicating risk to business stakeholders and developing organizational security strategy.
Ready to transform your vulnerability management? Schedule a demo to see Diligent ITRM in action.